Endpoints Configuration
The first and most essential step in preparing your production environment is to configure your application to connect to the exposed endpoints of your Resource Server.
Learn about the Resource Server implementation.
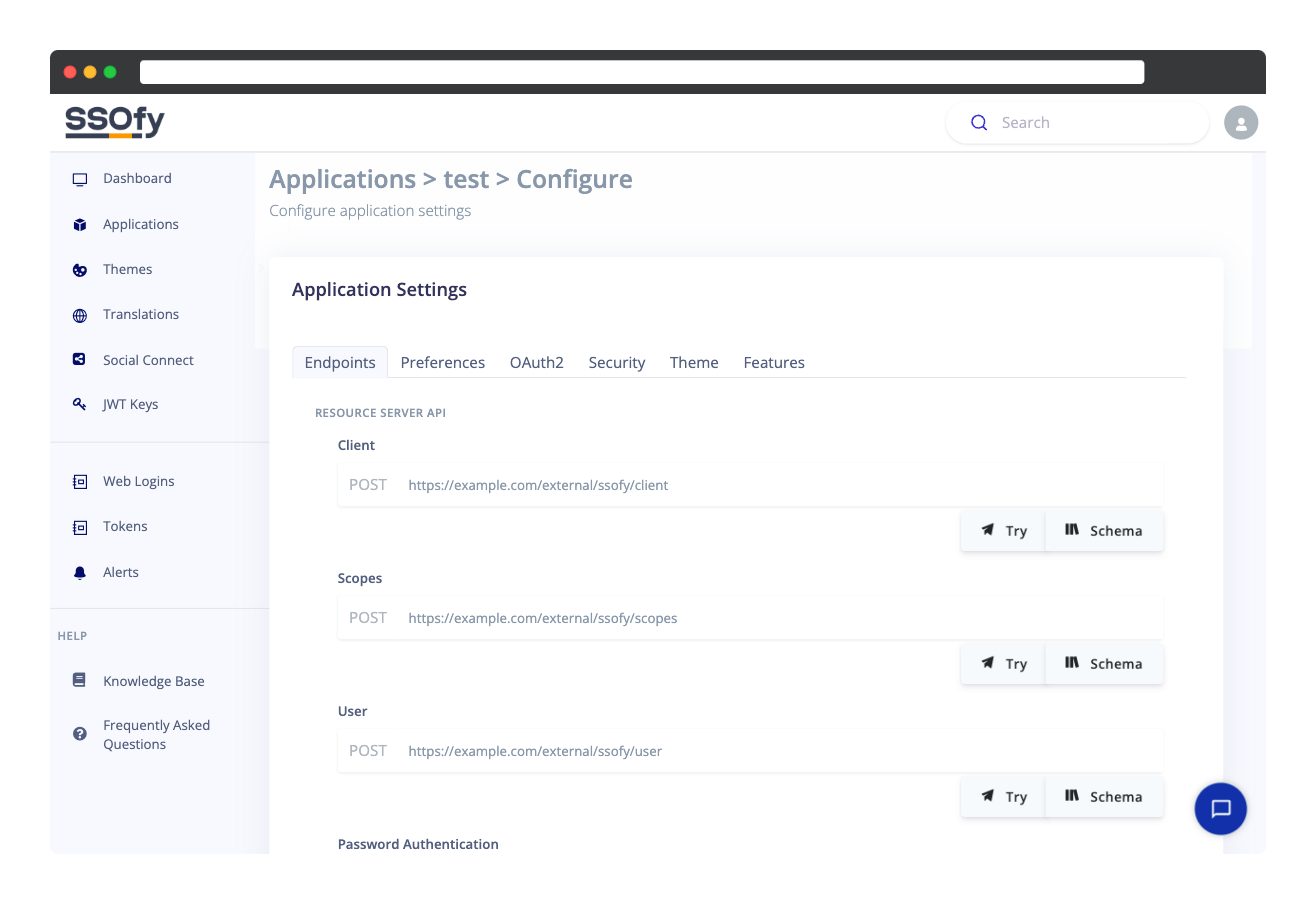
Make sure you have a running Resource Server providing the following publicly accessible endpoints:
Resource Server API
- requiredScopes: Scopes are the permissions that are requested or granted to an application to access certain resources on behalf of a user. These scopes define the level of access that an application has to a user's resources, and they are used to limit the amount of data that an application can access. For example, an application might request a scope to access a user's profile information, or to post updates on the user's behalf. The scopes are defined by the SSO server and can be customized based on the specific needs of the application.
- requiredClient: In OAuth2, a client is a front-end or back-end application that requests a token.
- requiredUser: SSOfy should be able to obtain user information in a variety of situations, such as in response to API queries like Resource Owner or Find User.
- optionalPassword Authentication: This endpoint will be used to authenticate users using their login identifier (email, username, etc.) and password.
- optionalToken Authentication: This is an optional endpoint for password-less authentication.
- optionalSocial Authentication: This an optional endpoint which will be used to find (authenticate) OR create a user after a successful login on a social provider (Google, Facebook, etc.) via an SSOfied login page.
- optionalOTP Options: When Two-factor Authentication is enabled for logins or password resets, SSOfy sends a request to the resource server to obtain available OTP options for verifying the user's identity by sending a confirmation code to their preferred method (email or sms).
- optionalEvents: There should be a single endpoint for receiving events.
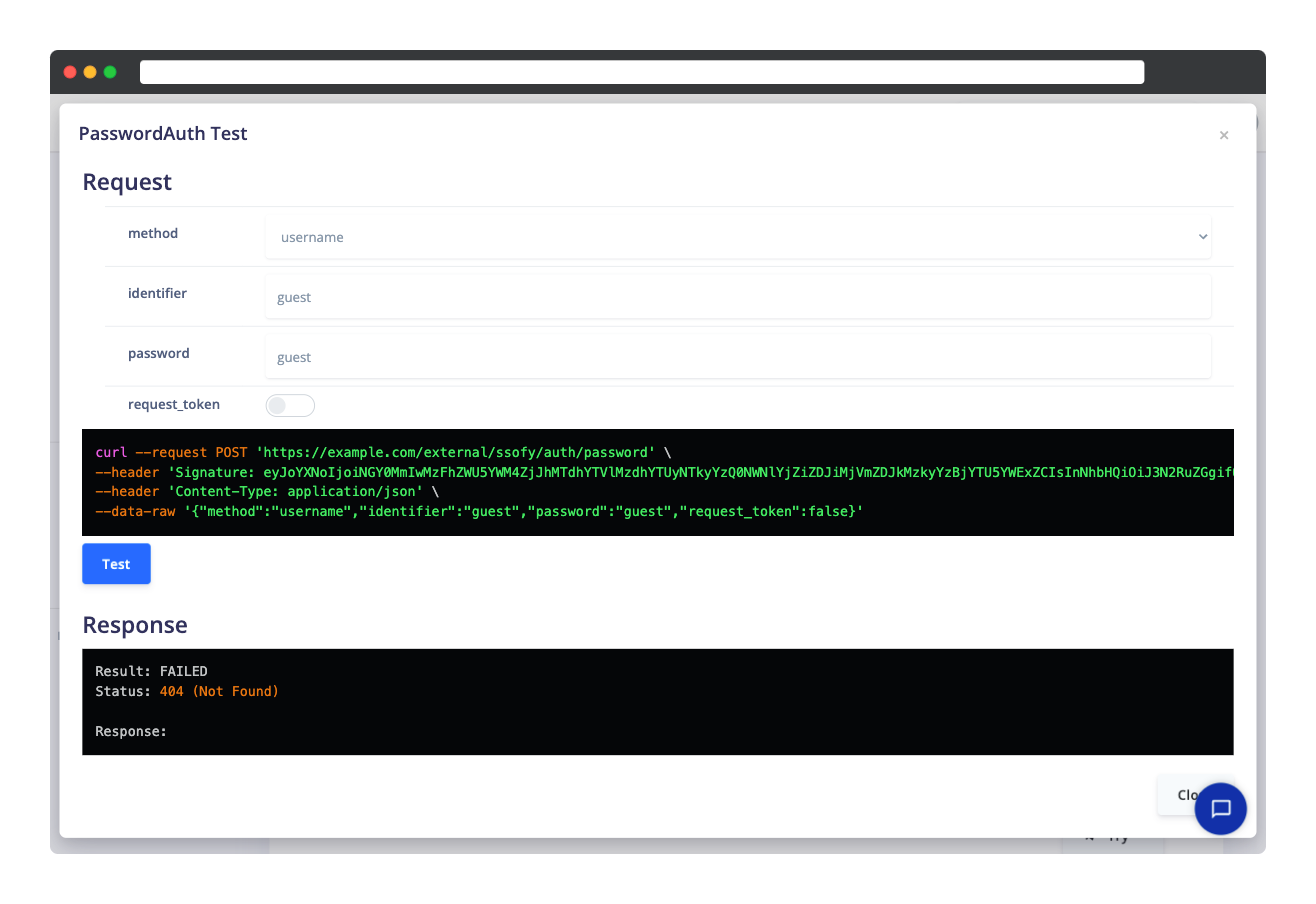
Test Utility
Next to each endpoint url box, you can notice a Try button. SSOfy includes a testing utility which helps you to debug and troubleshoot your endpoints by passing arguments and calculating the signature automatically.
The response payloads will be checked against each schema to ensure that your endpoints are providing legitimate responses in the same way that the SSO server verifies responses in production.
 Knowledge Base
Knowledge BaseAt our core, we believe that staying up-to-date with the latest trends and advancements in Authentication and related areas is essential. That's why we take great pride in keeping you informed with the latest insights, updates, and news in this rapidly evolving landscape.
Do you need support?
SSOfy is by Cubelet Ltd.
Copyright © 2025 Cubelet Ltd. All rights reserved.
Copyright © 2025 Cubelet Ltd. All rights reserved.